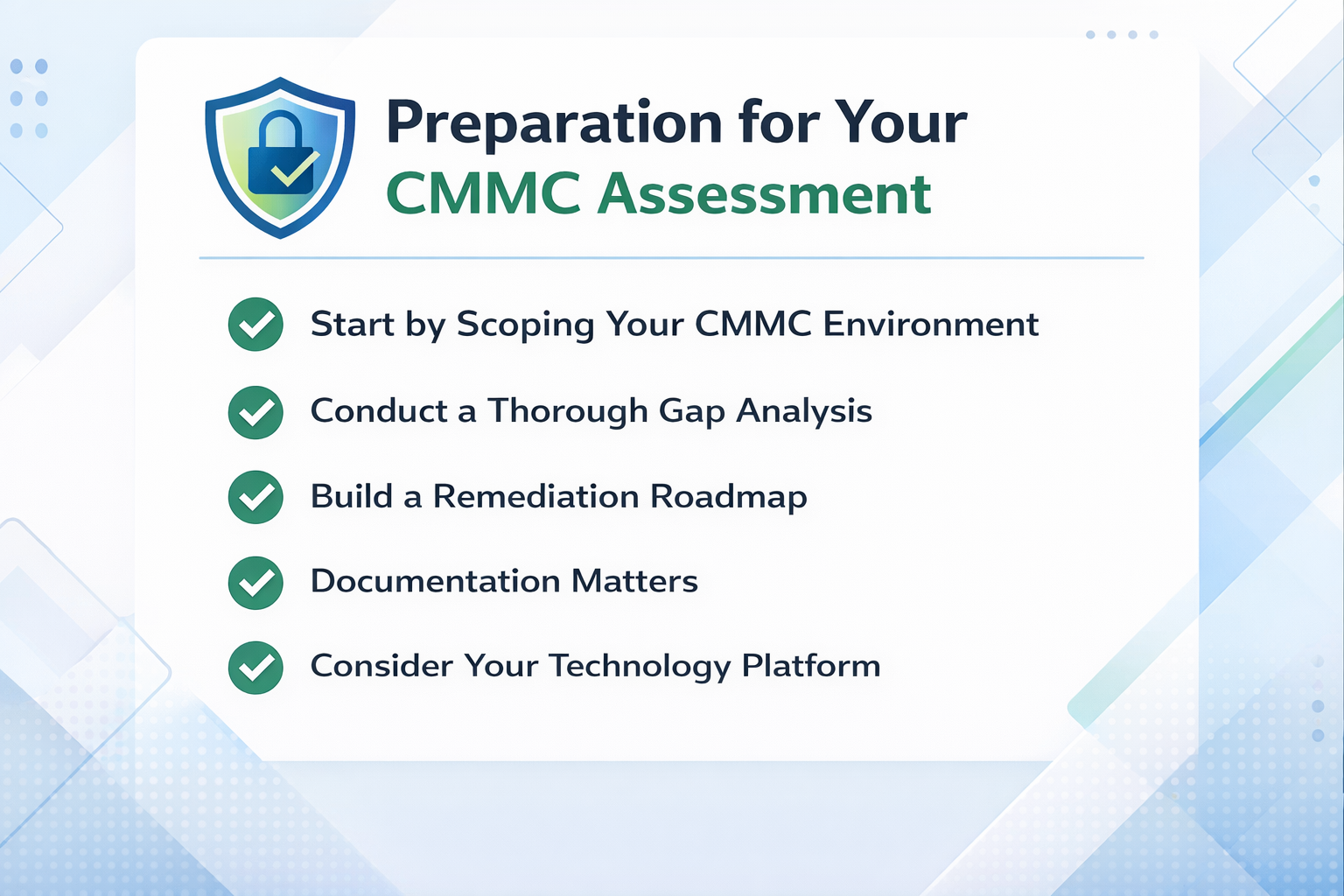
Meeting CMMC 2.0 requirements isn't something you can improvise six weeks before a contract deadline. Defense contractors who handle controlled unclassified information (CUI) are subject to a formal set of cybersecurity obligations that now carry real teeth — third-party audits, affirmations, and eventually mandatory inclusion in DoD contracts under DFARS 7012 and its successor clauses. This guide breaks down exactly what you need to do: the controls, the documentation, the technical work, and the assessment process — organized so an IT director or CISO can use it as a working roadmap.
Read MoreA program manager at a mid-sized defense contractor asks a simple question: "Can we use Copilot to summarize meeting notes about our Navy contract?" The IT director pauses. The contract references ITAR-controlled technical data. The company uses Microsoft 365 Commercial. The answer is no, not today, and the path to yes is longer than anyone wants to hear.
This scene plays out across the Defense Industrial Base every week. The pressure to adopt AI is real. So is the regulatory wall that separates commercial Microsoft 365 from environments allowed to touch Controlled Unclassified Information (CUI). Bridging the two is what Microsoft 365 Copilot deployment in GCC High readiness services are designed to do.
What GCC High Copilot Readiness Services Actually Cover
Read MoreDefense contractors facing CMMC compliance have a fundamental architecture decision to make before they spend a dollar on licensing or migration services. Should you move your entire organization into a Microsoft 365 GCC High tenant, or should you build a CMMC enclave that isolates only the users and systems that handle Controlled Unclassified Information (CUI)? The answer depends on how much of your business actually touches regulated data, what your contracts require, and how much complexity your IT team can realistically manage.
This guide compares both approaches so you can make the right call for your organization's compliance posture, budget, and operations.
Key Insights: What You Need to Know About CMMC Enclave vs. Full GCC High Migration
Read MoreIf your organization handles Controlled Unclassified Information (CUI) under a Department of Defense contract, you already know that Microsoft 365 GCC High is the cloud environment built for your situation. What most defense contractors underestimate is the true GCC High cost once you move past the per-user license fee and into the full picture of migration, operations, and long-term compliance.
This guide breaks down what GCC High actually costs for defense contractors, which Microsoft licensing options apply, and where the budget surprises tend to hide.
Key Insights: What You Need to Know About GCC High Cost and Licensing
Read MoreDefense contractors handling sensitive government data face a critical infrastructure decision that directly affects their eligibility for DoD contracts. Microsoft GCC High has emerged as the de facto standard cloud environment for organizations in the Defense Industrial Base working with Controlled Unclassified Information (CUI) and export-controlled data. If you're evaluating cloud platforms for CMMC compliance or wondering whether your current Microsoft 365 setup meets DoD requirements, understanding the distinction between GCC High and other Microsoft cloud offerings isn't optional-it's essential to your contract eligibility.
Key Insights for Defense Industrial Base (DIB) Compliance
Read MoreNative Integration Brings Seamless Governance and Security to AI Applications
For years, the story of enterprise AI has followed a predictable storyline: a promising use case receives approval, a development team builds something impressive, and then the project stalls. The reason is not that the technology failed, but rather that compliance could not keep up. Security reviews, data classification requirements, audit trails, retention policies, and governance work consistently take longer to complete than the actual development.
Microsoft recently announced native integration between Foundry and Purview, and for IT and security leaders who have been watching AI adoption intersect with compliance requirements, this is a development worth paying attention to.
What's Actually Changed
Read MoreThe regulatory countdown that defense contractors have been watching for years is finally over. On November 10, 2025, the Department of Defense began including CMMC 2.0 requirements in contract solicitations - transforming cybersecurity compliance from a policy goal into a binding contractual obligation for anyone in the defense supply chain. If you manufacture components for the DoD, provide engineering services, or operate anywhere in the defense industrial base, CMMC 2.0 compliance now directly determines whether you can bid on and win contracts.
Read MoreComparing Common Approaches to GCC High Migration
Introduction
Organizations that work with U.S. government contracts or handle sensitive regulated data often face tough decisions about their cloud strategy. Two common approaches for meeting requirements are migrating all users to a dedicated Microsoft GCC High tenant or creating a secure enclave and migrating only select users. This blog post explores the differences between these two strategies, highlighting the pros and cons of each so you can make an informed decision for your organization.
What Is GCC High?
Microsoft GCC High (Government Community Cloud High) is a dedicated cloud environment designed specifically for U.S. government agencies and contractors that must comply with strict regulatory standards, such as FedRAMP High, ITAR, and DFARS when handling controlled unclassified information (CUI). GCC High provides enhanced controls, data residency in the continental United States, and a dedicated infrastructure that separates government data from commercial environments.
What Is a Secure Enclave?
Read MoreMicrosoft has introduced Microsoft 365 Business Premium for GCC High, a tailored solution for small and mid-sized organizations in the Defense Industrial Base (DIB). This offering provides a cost-effective path to compliance with CMMC 2.0 and NIST 800-171, while maintaining the strict security and sovereignty standards of the GCC High environment.
✅ What Does GCC High Business Premium Include?
The new Business Premium for GCC High license mirrors much of the functionality of the commercial Business Premium suite but operates within Microsoft’s U.S. Government Community Cloud High (GCC-High) environment. Key features include:
Read MoreThe Cybersecurity Maturity Model Certification (CMMC) is on track to become a core requirement for defense contractors. However, before CMMC can be included in Department of Defense (DoD) contracts, a key regulation must take effect: Title 48 of the Code of Federal Regulations (48 CFR).
If your organization does business with the DoD—or hopes to—you need to understand this rule and how it will impact your eligibility to win and maintain government contracts.
What Is 48 CFR?
48 CFR is part of the Federal Acquisition Regulation (FAR) System, which governs how the federal government procures goods and services. Within this system, the Defense Federal Acquisition Regulation Supplement (DFARS) adds DoD-specific rules. The 48 CFR rule specifically integrates CMMC 2.0 into the DFARS. In short, this rule establishes cybersecurity requirements as a contractual obligation—not just policy guidance.
How 48 CFR Connects to CMMC 2.0
Read MoreSubscribe to Daymark Insights
Latest Posts
Browse by Tag
- Cloud (70)
- Microsoft (49)
- Security (47)
- Azure (37)
- Data Protection (32)
- Partners (32)
- Compliance (30)
- Data Center (29)
- Backup (26)
- CMMC (26)
- Daymark News (23)
- Storage (21)
- Data Governance (20)
- GCC High (18)
- Veritas (18)
- Virtualization (18)
- Cybersecurity (17)
- Featured Gov (15)
- Government Cloud (15)
- Cloud Backup (14)
- Disaster Recovery (14)
- Managed Services (13)
- AI (10)
- Industry Expertise (9)
- NIST SP 800-171 (6)
- Networking (6)
- Hybrid Cloud (5)
- Copilot (3)
- Pure Storage (3)
- Reporting (3)
- Services (3)
- AI for Defense (2)
- Cloud Security (2)
- Copilot (2)
- GDPR (2)
- CMMC 2.0 Requirements (1)
- FedRamp AI (1)
- Mobile (1)