The regulatory countdown that defense contractors have been watching for years is finally over. On November 10, 2025, the Department of Defense began including CMMC 2.0 requirements in contract solicitations - transforming cybersecurity compliance from a policy goal into a binding contractual obligation for anyone in the defense supply chain. If you manufacture components for the DoD, provide engineering services, or operate anywhere in the defense industrial base, CMMC 2.0 compliance now directly determines whether you can bid on and win contracts.
Read MoreComparing Common Approaches to GCC High Migration
Introduction
Organizations that work with U.S. government contracts or handle sensitive regulated data often face tough decisions about their cloud strategy. Two common approaches for meeting requirements are migrating all users to a dedicated Microsoft GCC High tenant or creating a secure enclave and migrating only select users. This blog post explores the differences between these two strategies, highlighting the pros and cons of each so you can make an informed decision for your organization.
What Is GCC High?
Microsoft GCC High (Government Community Cloud High) is a dedicated cloud environment designed specifically for U.S. government agencies and contractors that must comply with strict regulatory standards, such as FedRAMP High, ITAR, and DFARS when handling controlled unclassified information (CUI). GCC High provides enhanced controls, data residency in the continental United States, and a dedicated infrastructure that separates government data from commercial environments.
What Is a Secure Enclave?
Read MoreMicrosoft has introduced Microsoft 365 Business Premium for GCC High, a tailored solution for small and mid-sized organizations in the Defense Industrial Base (DIB). This offering provides a cost-effective path to compliance with CMMC 2.0 and NIST 800-171, while maintaining the strict security and sovereignty standards of the GCC High environment.
✅ What Does GCC High Business Premium Include?
The new Business Premium for GCC High license mirrors much of the functionality of the commercial Business Premium suite but operates within Microsoft’s U.S. Government Community Cloud High (GCC-High) environment. Key features include:
Read MoreThe Cybersecurity Maturity Model Certification (CMMC) is on track to become a core requirement for defense contractors. However, before CMMC can be included in Department of Defense (DoD) contracts, a key regulation must take effect: Title 48 of the Code of Federal Regulations (48 CFR).
If your organization does business with the DoD—or hopes to—you need to understand this rule and how it will impact your eligibility to win and maintain government contracts.
What Is 48 CFR?
48 CFR is part of the Federal Acquisition Regulation (FAR) System, which governs how the federal government procures goods and services. Within this system, the Defense Federal Acquisition Regulation Supplement (DFARS) adds DoD-specific rules. The 48 CFR rule specifically integrates CMMC 2.0 into the DFARS. In short, this rule establishes cybersecurity requirements as a contractual obligation—not just policy guidance.
How 48 CFR Connects to CMMC 2.0
Read MoreOn October 15, 2024, the final rule for the Cybersecurity Maturity Model Certification (CMMC) program was officially published. This rule, codified as 32 CFR, becomes effective on December 16, 2024. The CMMC journey began in 2019 with DFARS Case 2019-D041, and after four years of development, the rule is now finalized. Let’s take a look at the history of the CMMC timeline, what's to come, and how organizations can prepare for what is next.
CMMC Rulemaking Timeline
The rulemaking process illustrated in the graphic below shows a high-level workflow from the Government Accountability Office (GAO).
Figure 1: GAO Federal Rulemaking
Read MoreProtecting sensitive and classified information when working for the Federal Government requires constant vigilance. When the government issues a contract, it must specify to the performing contractor when covered defense information (CDI) or controlled unclassified information (CDI) will be generated under the contract. Many prime contractors “flowdown” every FAR and DFARS clause to subcontractors and vendors without considering if that subcontractor or vendor will be processing, storing, or transmitting CDI. Anticipating where CDI may reside once awarded a contract can be a challenge. Here is guidance on ways CDI can flowdown to subcontractors and the defense industrial base (DIB), and steps those organizations should take before signing an agreement.
An Introduction to DFARS
Read MoreMany companies are currently evaluating how they might fund initiatives necessary to move their businesses towards compliance with the Cybersecurity Maturity Model Certification (CMMC). There are a few ways to fund these initiatives, but many key items have the potential to impact the amount of funding needed to prepare your organization for certification. So, where do you start to appropriately scope the project, and how do you know how much it will actually cost?
Whether your company plans to meet the CMMC objectives or to stop doing business with the Federal Government, keep in mind that cybersecurity is an important part of maintaining your business health and ensuring resiliency in the future. When businesses suffer a cyberattack and cannot afford the cost to recover, they often go bankrupt. In addition to the new federal regulations being pushed out by the Defense Federal Acquisition Regulations (DFARS), many states have laws requiring levels of protection for different types of information. Other federal governments have also enacted cybersecurity protection measures for their citizens (such as GDPR). Not doing so can also leave you open to lawsuits in the event of a breach or incident.
5 Phases for Cybersecurity Compliance
Read MoreGovernment organizations today face an unprecedented need for innovation and efficiency. From delivering public services to safeguarding national security, the challenges are immense, and the stakes are high. This is where Microsoft's Azure for US government (Azure Government), a proven and trusted cloud for US government agencies, in conjunction with Azure OpenAI, can step in as a transformative force. In this blog post, I’ll explore why government agencies and organizations that support the government should be taking note of the capabilities and benefits of Azure Government with Azure OpenAI.
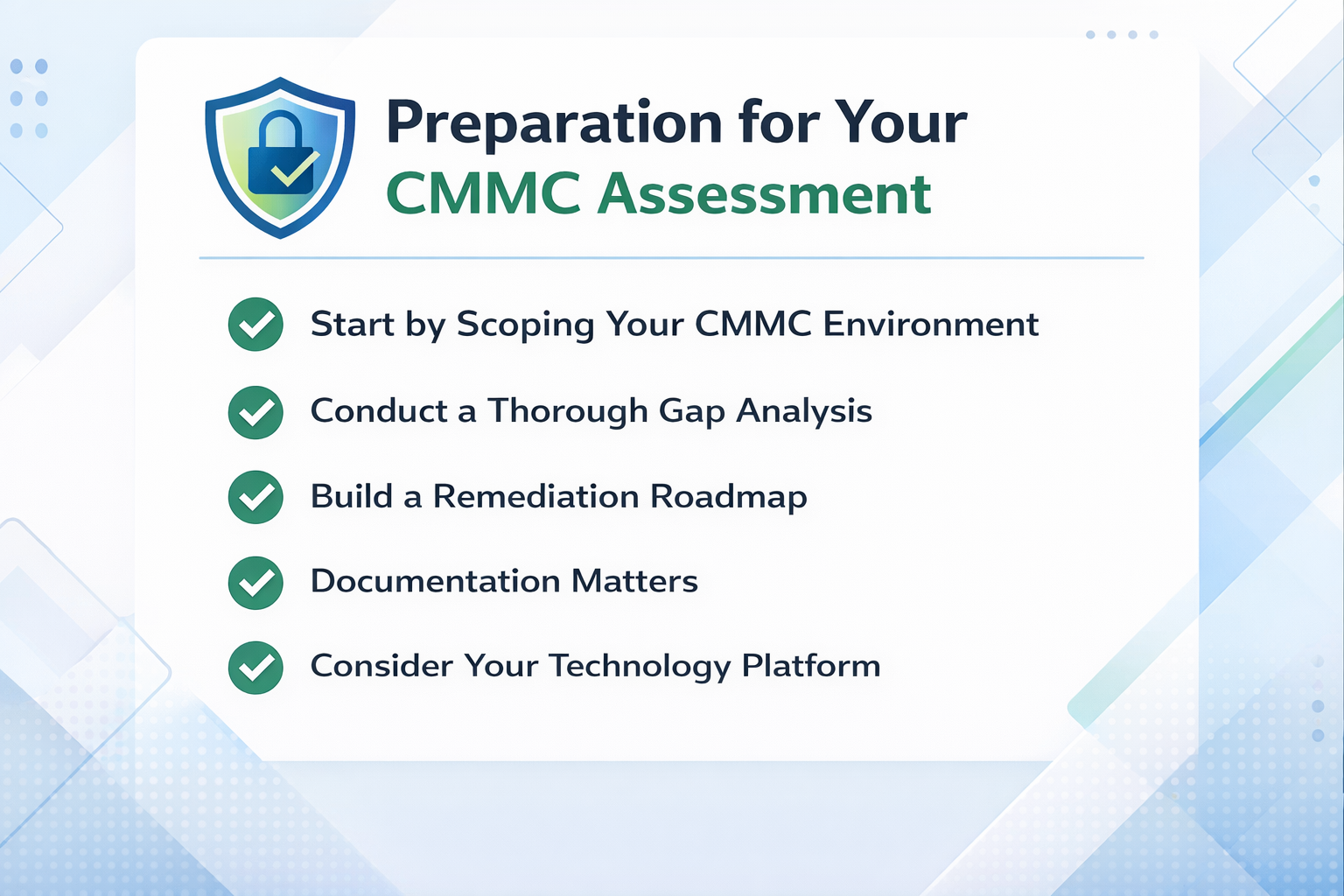
Read MoreThe Cybersecurity Maturity Model Certification (CMMC) 2.0 is the DoD framework designed to enhance cybersecurity and protect against compromise of sensitive defense information on contractors’ systems. Some defense industrial base organizations (DIB) have mistakenly taken a “wait and see” attitude about preparing for CMMC compliance, believing that they will wait until the government finalizes 2.0 requirements. While holding off on the time, resources and budget to prepare for CMMC may seem prudent (and frankly easier to delay), the risks of waiting could have a significantly negative impact on contractors’ revenue. Here’s why:
Read MoreIf your organization has been working towards NIST 800-171 and is now on the journey to achieve CMMC 2.0 (the Cybersecurity Maturity Model Certification) it can be difficult to understand what you’ve already achieved and what’s left to do. Both standards are intended to reduce threats and strengthen cybersecurity for sensitive government data. Here’s some details on how they relate to each other and what’s involved to take the next steps toward CMMC compliance.
Read MoreSubscribe to Daymark Insights
Latest Posts
Browse by Tag
- Cloud (70)
- Microsoft (49)
- Security (47)
- Azure (36)
- Data Protection (32)
- Partners (32)
- Compliance (29)
- Data Center (28)
- Backup (26)
- CMMC (24)
- Daymark News (23)
- Data Governance (20)
- Storage (20)
- Veritas (18)
- Virtualization (18)
- Cybersecurity (17)
- GCC High (16)
- Cloud Backup (14)
- Disaster Recovery (14)
- Government Cloud (14)
- Featured Gov (13)
- Managed Services (13)
- AI (10)
- Industry Expertise (9)
- Networking (6)
- Hybrid Cloud (5)
- NIST SP 800-171 (5)
- Reporting (3)
- Services (3)
- Cloud Security (2)
- Copilot (2)
- Copilot (2)
- GDPR (2)
- Pure Storage (2)
- AI for Defense (1)
- FedRamp AI (1)
- Mobile (1)