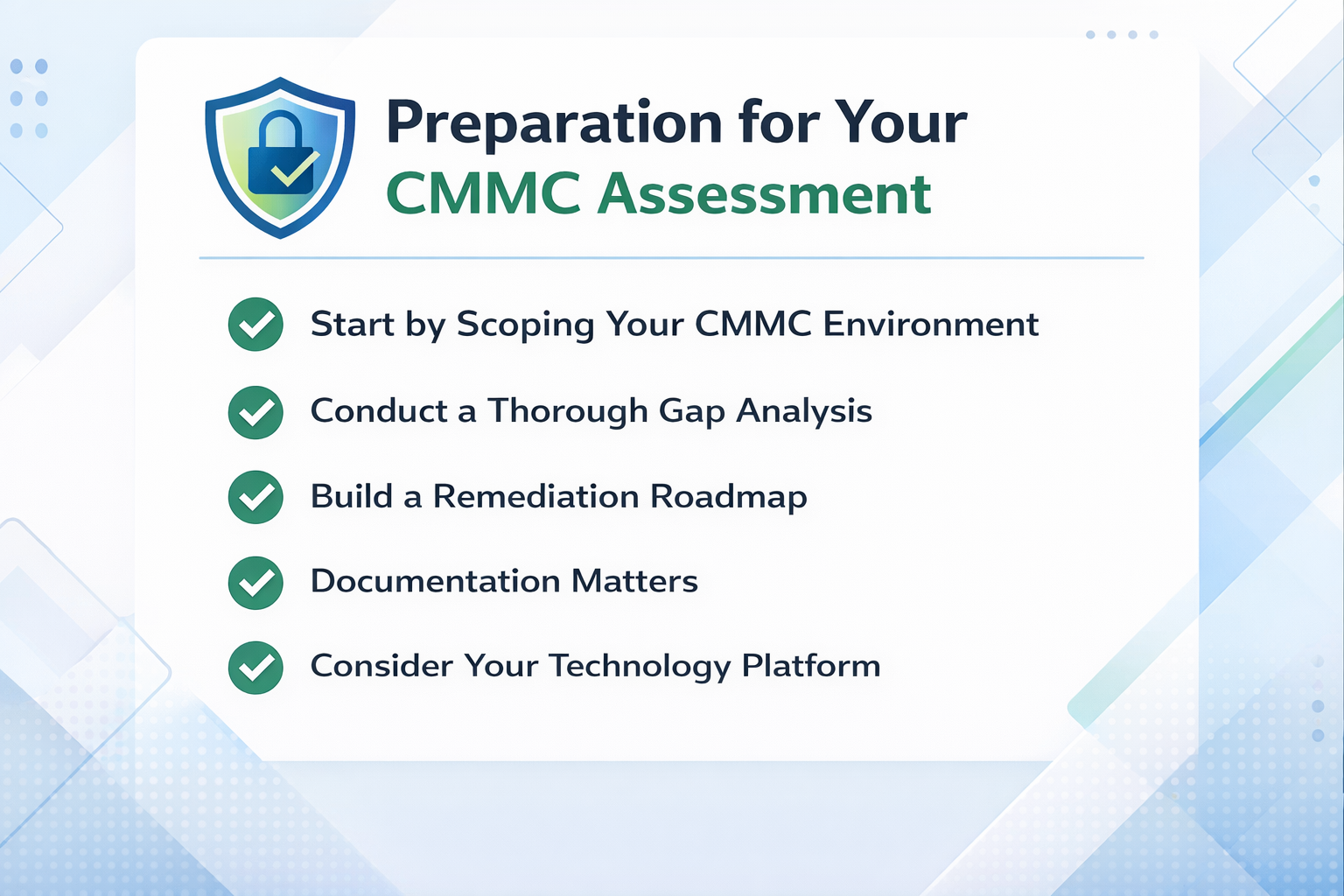
Defense contractors facing CMMC compliance have a fundamental architecture decision to make before they spend a dollar on licensing or migration services. Should you move your entire organization into a Microsoft 365 GCC High tenant, or should you build a CMMC enclave that isolates only the users and systems that handle Controlled Unclassified Information (CUI)? The answer depends on how much of your business actually touches regulated data, what your contracts require, and how much complexity your IT team can realistically manage.
This guide compares both approaches so you can make the right call for your organization's compliance posture, budget, and operations.
Key Insights: What You Need to Know About CMMC Enclave vs. Full GCC High Migration
Read More





.png)