
Properly securing assets is a constant challenge for IT. Staying one step ahead of the bad actors is a never-ending job and with a well-known shortage of IT security professionals, it’s critical that those of us responsible for protecting systems, networks and data are smart about deploying tools that will help remediate or minimize cybersecurity risks. Microsoft built Azure Security Center to help. It aligns Azure resources with Microsoft best practices to mitigate risks associated with security vulnerabilities that could lead to a breach or other security incident.
Microsoft Security Quick Facts
Microsoft has made security a top priority by:
- Investing more than $1 billion annually on cybersecurity research and development
- Employing more than 3,500 security experts dedicated to data security and privacy
- Providing more compliance certifications for Azure than any other cloud provider
Here’s Microsoft’s definition of Azure Security Center: “Azure Security Center is a unified infrastructure security management system that strengthens the security posture of your data centers, and provides advanced threat protection.”
In the cloud world, you can bring workloads into Azure through IaaS and PaaS to name a few. Security Center reaches across all of Microsoft’s offerings so that it can easily adapt to rapidly changing workloads. And it does so with a continuous assessment across the entire environment.
As attacks become more sophisticated and frequent, leveraging Microsoft’s team of security experts becomes invaluable and can help you address:
- Rapidly changing workloads
- Increasingly sophisticated attacks
- Security skills shortages
Microsoft Rebranding
Please note there was quite a bit of rebranding and repackaging by Microsoft on the security front and it can get a bit confusing. Here’s how it all morphed:
Advanced threat protection or ATP products for M365 have all been aligned under Microsoft Defender:
- Microsoft Defender for Endpoint (previously Microsoft Defender Advanced Threat Protection)
- Microsoft Defender for Office 365(previously Office 365 Advanced Threat Protection)
- Microsoft Defender for Identity(previously Azure Advanced Threat Protection)
Azure solutions were aligned as well:
- Azure Defender for Servers(previously Azure Security Center Standard Edition)
- Azure Defender for IoT(previously Azure Security Center for IoT)
- Azure Defender for SQL(previously Advanced Threat Protection for SQL)
The goal was to create a simpler naming scheme, but if you were used to some of the older ATP (Advanced Threat Protection) language it can take some getting used to.
Cloud Native Security
Azure Security Center is natively part of Azure. As resources are deployed, recommendations will start appearing in Azure Security Center for your environment.
There are additional client-side agents for IaaS and they are typically auto-provisioned, but they can also be manually installed.
What’s really interesting is that you can extend security center to non- Azure systems. This requires some work building a log analytics workspace and deploying agents, but it is a great opportunity to have Security Center span a hybrid environment.
When you enable Security Center, it activates a built-in initiative within Security Center containing audit policies only. Some of you may have seen this policy already with the ASC prefix.
Tiers of Service
Microsoft offers two tiers of service. Azure Defender has become the “paid” version of Security Center.
The free experience includes features such as secure score, detection of security misconfigurations in your Azure machines and asset inventory. When you upgrade to Azure Defender you get a whole host of features. The pricing does vary from resource to resource. We’ll get into that later.
Justifications to make the move to Defender include:
- Just in time VM access - which provides the ability to turn on access to minimize your attack surface
- Threat protection which relates directly back to the “security alerts” when going through the blades. (On a personal note, I remember installing gen2 SIEM’s and wishing the process was this clean back then.)
- Regulatory compliance for dashboards and reports. Currently there is support for Azure CIS, PCI DSS 3.2, ISO 27001, and SOC TSP. This enables the blade in Security Center to view your assessments and act on recommendations to reduce compliance gaps.
My experience has been that Just in Time access and the Threat protection are powerful enough features to justify the upgrade to Defender.
It’s worth noting that Azure Defender can either be turned on for the resource or the subscription. So, you don’t need to enable Azure Defender for all resources. And of course, Microsoft is quite experienced at getting users “hooked” and offers the first 30 days of Azure Defender free. I would highly suggest using this trial to test drive the compliance dashboard and/or see what Threat Protection can find in your environment for a month at no cost. It’s a worthwhile investment of your time.
Secure Score
I highly recommend using Secure Score as a gauge for the general security health of your environment and of course tracking it. In many ways, security is the job that is never complete. But Secure Score takes the job of securing your environment measurable to the Microsoft standard. Microsoft has been able to distill an overall security posture into a single value. This has always been the holy grail of explaining systems compliance in an environment. I would recommend integrating this value into security reports or executive summaries.
Dashboard Overview
The getting started area is great for upgrades, installing agents or just general information. It provides the rough prices for resources running. Most of these are a flat rate like VMs. Azure Defender for servers is around $14.60 a month for 500 MB a day. Granted, costs can be more expensive if there’s more than 500 MB a day of processing. Also, for resources like storage accounts it’s a transactional cost.
Inventory
Inventory provides a dashboard of your resources and lets you know what it considers unhealthy and highlights the severity of recommendations for each resource. From here, you can create files and export to a csv if required. You can also “add non-Azure servers.”, as stated prior it’ s possible to extend Azure Security Center to on-premises data centers through an agent install.
In the ASC community there are playbooks, automation scripts, remediation templates and custom recommendations. This GitHub link is a great place to start developing a basic Security Center setup.
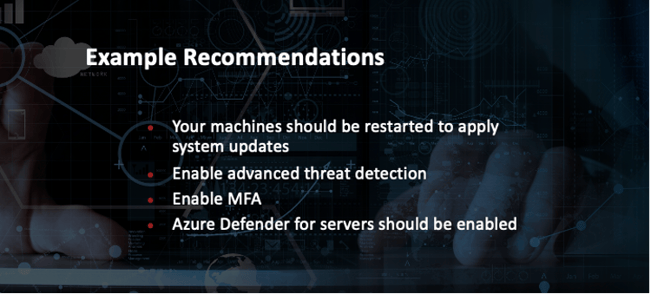
Recommendations
Recommendations are at the core of Azure Security Center. These dictate what changes would put your security practices in line with Microsoft best practices. Below are some examples of common recommendations.
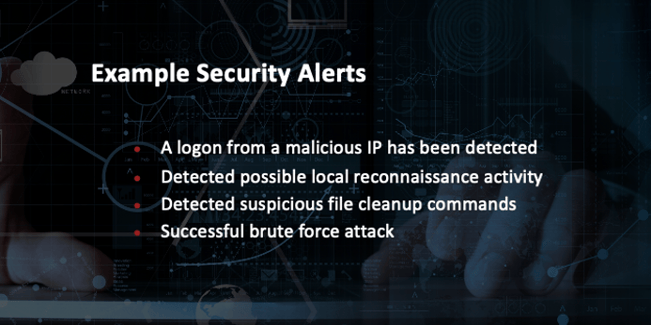
Security Alerts
Alerts are enabled when upgrading to the Defender level of protection. Below are a few examples of security alerts that have been enabled.
Suppression Rules
Suppression rules are found in the security alerts dashboard where you can quickly see all alerts and then decide to dismiss or create suppression rules. What’s great about suppression rules is you can set it to a variety of different values like user or resource. You can also annotate rules with notes and set a rule expiration.

A well-engineered cloud offering will quickly adapt to change. So, if you are going to be dipping your toes deeper into Security Center it’s always a good idea to take a look at the Azure updates site. It provides a wealth of information and you can even get these as an RSS feed.
Be warned there is such a thing as “death by updates” -- I prefer checking once a month and doing a quick search to find any applicable changes. Alternatively, you can always select the “what’s new” button from the Security Center overview page.
Strategies for Success
Recapping strategies for success and decision points:
- Free versus Defender - Remember Defender has JIT, advanced threat alerts and analysis as well as some great compliance dashboards
- Remediate or Exemptions for Recommendations – Remediate wherever possible and place exceptions when it makes sense
- Setup Security Alerts – Enable alerts while also Creating Suppression Rules to block out any noise
- Track your Scores – Scores create a measurable metric to roughly track alignment with Microsoft Best Practices for security
- Azure Updates – Keep up with the constantly-changing threat landscape
- GitHub Community – Check out the community for custom templates and scripts
Benefiting from Microsoft’s Breadth and Depth
Microsoft security researchers are constantly on the lookout for threats. Because of their global presence in the cloud and on-premises, they have access to an expansive set of telemetry. The wide-reaching and diverse collection of datasets enables Microsoft to discover new attack patterns and trends. As a result, Security Center can rapidly update its detection algorithms as attackers release new and increasingly sophisticated exploits. This approach helps you keep pace with a fast-moving threat environment.
To detect real threats and reduce false positives, Security Center collects, analyzes, and integrates log data from your Azure resources and the network. It also works with connected partner solutions, like firewall and endpoint protection solutions. Security Center analyzes this information, often correlating information from multiple sources, to identify threats.
Daymark Cloud Clinic Webinars
Azure Security Center was a topic we covered at one of our Daymark Cloud Clinic sessions – a series of complimentary training webinars. In addition, we’ve covered Continuous Access Evaluation (CAE), Azure Reserved Instances and Azure Sentinel to explain how these features work. We’ll be hosting more Cloud Clinics in 2021. Follow us on Twitter @Daymarksi to keep up with new topics and dates.



