
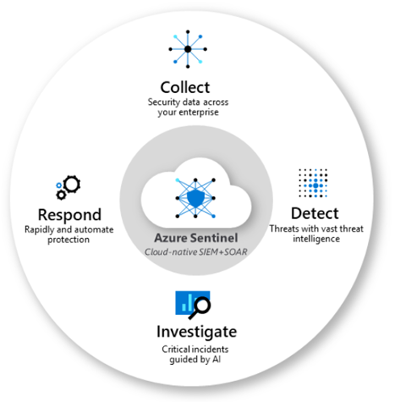
Azure Sentinel is a cloud native Security Information Event Management (SIEM) and Security Orchestration, Automation and Response (SOAR) solution from Microsoft. It was the topic of discussion at one of our recent Daymark Cloud Clinics where our technical cloud consultants offer complimentary technical training and tips on a wide range of Azure and Office 365 features.
SOAR vs. SIEM
SOAR refers to a collection of software solutions and tools that allow organizations to streamline security operations in three key areas: threat and vulnerability management, incident response, and security operations automation. An SIEM solution aggregates data and provides real-time analysis of security alerts generated by applications and network appliances. It’s common for IT professionals to mix up the capabilities of SIEM and SOAR since they tend to work together with a goal of protection. In fact, traditionally, they were two separate products or components, however Microsoft designed Azure Sentinel to handle both SIEM and SOAR in a single solution.
How Sentinel Works
First, devices and services need to start streaming their data into Sentinel, via Data Connectors. Technically, the data flows into Azure Log Analytics. Workbooks are used to visualize the data, potential issues and trends, and help create specific queries. These queries can help create rules called analytics. After creating analytic rules, you start to see Incidents, as well as process automated actions via Playbooks. When analyzing Incidents, you can leave a trail of Bookmarks to flag interesting or anomalous data for follow up and discover other areas that may be affected. Finally, and after gaining experience, you can go hunting for threats.
Diving into the Details
Microsoft has created built-in queries and Analytics and so it’s unlikely that you would need to create your own out of the box, however as you progress you could find a need for something more specific for your organization’s security needs. If so, here are more detailed explanations:
Log Analytics – All data ingested into Azure Sentinel must come from a Log Analytics workspace. A workspace is basically a limitless storage container that holds all your data from a variety of sources. It is recommended to have a single, dedicated workspace created for Azure Sentinel.
Workbooks – Provide a means of monitoring the data that has been ingested into Azure Sentinel. Built-in workbooks allow you to evaluate data immediately. Custom workbooks can also be created to allow you to view your data the way you need to.
Analytics – Custom rule sets that can be created to search across all ingested data to discover potential threats. There are many pre-built rules provided as well as connections to Microsoft sources such as Microsoft Defender ATP and Cloud App Security. Additional custom rules can be created based on queries. These can run on a scheduled interval. All hits from each rule can generate an incident and/or run a playbook.
Incidents – Alerts that are generated based on Analytics rule sets. An incident can contain multiple alerts. They allow for further investigation to determine if there were additional areas of exposure using the investigation graph. Incidents can be assigned to a specific individual to delegate the investigative tasks.
Playbooks – Playbooks are essentially Azure Logic Apps with specific designation to Azure Sentinel alerts. They allow for an orchestrated and automated response to alerts that are triggered via Analytics. Anything that you can do within a new or existing Logic App can also be extended to run based on an Azure Sentinel alert.
Notebooks – Azure Sentinel has integrated Jupyter notebooks directly into the Azure Portal. A notebook is a web application integrated into your browser that allows you to have live visualizations and code\queries running directly within the browser. A few notebooks are provided by Microsoft to illustrate their capabilities.
Hunting – Hunting allows for manual, proactive investigations into possible security threats based on the ingested data. Microsoft provided several built-in queries and custom queries can also be created. Once a query is created you can convert it into an analytic task to run on a schedule. Hunting capabilities include: Queries (using Kusto Query Language), Notebooks, Bookmarks, Live Stream
I hope that gives you a good idea of what Sentinel is all about and how to make the most of its capabilities. If you want to learn more about Microsoft security features, I suggest you check out or blog "An Inside Look at Azure Security."



